DNS Abuse Metrics & Trends

In a recent presentation to CENTR, our CTO, Lars Forsberg, outlined some findings from our DNS Abuse data set. In this article we dig into those findings and share some key metrics and trends.
Before We Begin
DNS Abuse has been a hot topic in the industry for quite some time now. And everyone has an opinion about what "DNS Abuse" is.
To make clear what this article is referring to, the definition used here is from the DNS Abuse Framework's definition of DNS Abuse. The framework states that DNS Abuse is: Malware, Botnets, Phishing, Pharming, and Spam (when it serves as a delivery mechanism for the other forms of DNS Abuse).
Any statistics and data quoted here, are filtered to only include these categories of malicious behaviour.
Source of DNS Abuse Data
The data presented to you today is taken from a unified source of DNS Abuse reports, collected from 9 different threat intelligence feeds, which are all vetted on an ongoing basis.
The feeds have been selected from a list of over 200, based on their overall quality, low false positive rate and their relative freshness of data. These feeds are: Malware Patrol, Anti-Phishing Working Group, SURBL, Spamhaus, Google Webrisk, CRDF Threat Center, OpenPhish, PhishTank, URLHaus.
Data has been collected from these feeds since 2018, with some being added at a later date than others. The latest addition was CRDF Threat Center, in early 2022.
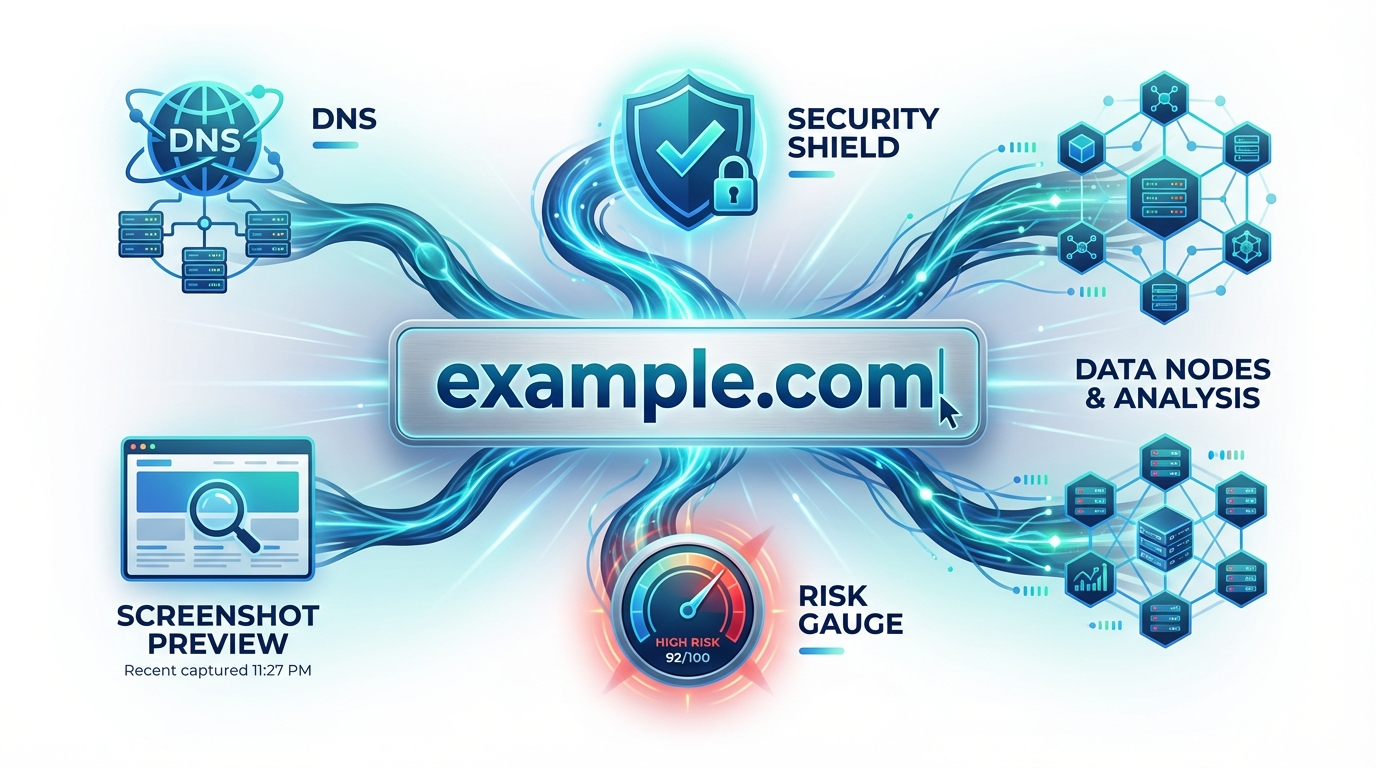
Today, iQ uses this data source to provide more than 175 TLDs, Registrars and Hosters with malicious activity updates on an hourly basis. Together these organisations make up for more than half the domain names registered, 201 Million.
Note: The DNS Abuse Feed does not implement sources that share data with each other and each report is thus unique in its origin.

DNS Abuse Metrics & Trends
As of the 1st of October 2022, the feed is tracking 2.4 million reports of DNS Abuse regarding 910 000 unique domain names. Each domain name in the feed has an average of 2.6 reports.
This means that, on average, one in every 368 domain names is associated with DNS Abuse. This is one of the metrics that iQ actively uses to compare different actors on their progress in mitigating abuse.
Compared to the beginning of the year, when there was a total of 2.1 million reports and 1.1 million domain names, this is a slight improvement, and a sign that more of the data sources are finding the same bad actors.

Top Categories
Looking at the different categories of DNS Abuse, Phishing (46%) and Spam (44%) are the most prevalent with Malware (8%) picking up third place. This has remained more or less stable for the last two consecutive years. As always, this is not an exact science, as more effort is being put into identifying the two leading categories than any other.
Another important fact is that Botnet and Malware is becoming more and more interchangeable as the vast majority of Malware is in some way connected to one botnet or another. Different sources categories and track these differently.
Lastly, Pharming, which is mentioned in the DNS Abuse Framework as a category, is hardly ever tracked by sources anymore as it is a two-factor attack that starts with malware being installed on a client computer, after which the user is sent to a Phishing site masked by the malware.

DNS Abuse Across TLDs?
Turning our view to the top-level domain names, there are currently at least one report of DNS Abuse for 928 different TLDs. With the fact that there is roughly 1500 domain names in the root zone, and that 600 TLDs are, due to their nature, not available for registration, it’s safe to say that the vast majority of all top-level domain names has DNS Abuse occurring them right now.
The amount of DNS Abuse is somewhat tied to the popularity of the TLD, as well as the availability, pricing, preventative measures and reputation of mitigation efforts, but all of this becomes irrelevant when looking into DNS Abuse on compromised domains, where all TLDs are more or less equally interesting for malicious actors.
Name and shame?
The landscape of which TLDs and Registrars have the most reports changes very rapidly, and more than 50 000 reports are created daily, which almost the same amount as those being closed, 47 900.
Therefore, naming and shaming makes little sense. Especially, if it's done without taking other factors, like zone size, availability and pricing into consideration.
In Summary
While a slight improvement has been noticed bad actors move fast. Continued vigilance, the sharing of data and expertise with industry colleagues is key.
DNS Abuse is a problem for all providers on the internet, and the least everyone can do is make themselves aware of the problem and their own situation.
There are many free sources of information out there and iQ provides one such resource at iQ Abuse Stats
If you have any questions on this article, or want to share your expertise and thoughts, please let us know!