"What Is.." Series - Understanding Malware (part 2)

In our previous post, we discussed what Malware is and what we can do to reduce risk.
In part 2, we will provide ways to prevent malware from being delivered and spreading, and how prepare for an incident.
Prevent Malware from being delivered and spreading to devices
You can reduce the likelihood of malicious content reaching your devices through a combination of:
- filtering to only allow file types you would expect to receive
- blocking websites that are known to be malicious
- actively inspecting content
- using signatures to block known malicious code
These are typically done by network services rather than users' devices. Examples include:
- mail filtering (in combination with spam filtering) which can block malicious emails and remove executable attachments.
- intercepting proxies, which block known-malicious websites
- internet security gateways, which can inspect content in certain protocols (including some encrypted protocols) for known malware
- safe browsing lists within your web browsers which can prevent access to sites known to be hosting malicious content
Ransomware is increasingly being deployed by attackers who have gained access remotely via exposed services such as Remote Desktop Protocol (RDP), or unpatched remote access devices. To prevent this organisations should:
- disable RDP if it's not needed
- enable MFA at all remote access points into the network, and enforce IP allow listing using hardware firewalls
- use a VPN for remote access to services; Software as a Service or other services exposed to the internet should use Single Sign-On (SSO) where access policies can be defined
- use the least privilege model for providing remote access - use low privilege accounts to authenticate, and provide an audited process to allow a user to escalate their privileges within the remote session where necessary
- patch known vulnerabilities in all remote access and external facing devices immediately, and follow vendor remediation guidance including the installation of new patches as soon as they become available
Prevent malware spreading across your organisation. You should also:
- use MFA to authenticate users so that if malware steals credentials they can't easily be reused
- ensure obsolete platforms (Operating Systems (OS) and apps) are properly segregated from the rest of the network
- regularly review and remove user permissions that are no longer required, to limit the malware's ability to spread
- ensure system administrators avoid using their accounts for email and web browsing (to prevent malware being able to run with their high level of system privilege)
- practice good asset management, including keeping track of which versions of software are installed on your devices so that you can target security updates quickly
- keep devices and infrastructure patched, especially security-enforcing devices on the network boundary (such as firewalls and VPN products)
Prevent Malware From Running On Devices
A 'defence in depth' approach assumes that malware will reach your devices. You should therefore take steps to prevent malware from running. The measures required will vary for each device type, OS and version, but in general you should look to use device-level security features. Organisations should:
- centrally manage devices in order to only permit applications trusted by the enterprise to run on devices, using technologies including AppLocker, or from trusted app stores (or other trusted locations)
- consider whether enterprise antivirus or anti-malware products are necessary, and keep the software (and its definition files) up to date
- provide security education and awareness training to your people
- disable or constrain scripting environments and macros, by:
- enforcing PowerShell Constrained Language mode via a User Mode Code Integrity (UMCI) policy - you can use AppLocker as an interface to UMCI to automatically apply Constrained Language mode
- protecting your systems from malicious Microsoft Office macros
- disable autorun for mounted media (prevent the use of removable media if it is not needed)
In addition, attackers can force their code to execute by exploiting vulnerabilities in the device. Prevent this by keeping devices well-configured and up to date. We recommend that you:
- install security updates as soon as they become available in order to fix exploitable bugs in your products
- enable automatic updates for OSs, applications, and firmware if you can
- use the latest versions of OSs and applications to take advantage of the latest security features
- configure host-based and network firewalls, disallowing inbound connections by default
Prepare For An incident
Malware attacks, in particular ransomware attacks, can be devastating for organisations because computer systems are no longer available to use, and in some cases data may never be recovered. If recovery is possible, it can take several weeks, but your corporate reputation and brand value could take a lot longer to recover.
The following will help to ensure your organisation can recover quickly.
- Identify your critical assets and determine the impact to these if they were affected by a malware attack.
- Plan for an attack, even if you think it is unlikely. There are many examples of organisations that have been impacted by collateral malware, even though they were not the intended target.
- Develop an internal and external communication strategy. It is important that the right information reaches the right stakeholders in a timely fashion.
- Determine how you will respond to the ransom demand and the threat of your organisation's data being published.
- Ensure that incident management playbooks and supporting resources such as checklists and contact details are available if you do not have access to your computer systems.
- Identify your legal obligations regarding the reporting of incidents to regulators, and understand how to approach this.
- Exercise your incident management plan. This helps clarify the roles and responsibilities of staff and third parties, and to prioritize system recovery. For example, if a widespread ransomware attack meant a complete shutdown of the network was necessary, you would have to consider:
- how long it would take to restore the minimum required number of devices from images and re-configure for use
- how you would rebuild any virtual environments and physical servers
- what processes need to be followed to restore servers and files from your backup solution
- what processes need to be followed if onsite systems and cloud backup servers are unusable, and you need to rebuild from offline backups
- how you would continue to operate critical business services
After an incident, revise your incident management plan to include lessons learnt to ensure that the same event cannot occur in the same way again.
Steps To Take If Your Organisation Is Already Infected
If your organisation has already been infected with malware, these steps may help limit the impact:
- Immediately disconnect the infected computers, laptops or tablets from all network connections, whether wired, wireless or mobile phone based.
- In a very serious case, consider whether turning off your Wi-Fi, disabling any core network connections (including switches), and disconnecting from the internet might be necessary.
- Reset credentials including passwords (especially for administrator and other system accounts) - but verify that you are not locking yourself out of systems that are needed for recovery.
- Safely wipe the infected devices and reinstall the OS.
- Before you restore from a backup, verify that it is free from any malware. You should only restore from a backup if you are very confident that the backup and the device you're connecting it to are clean.
- Connect devices to a clean network in order to download, install and update the OS and all other software.
- Install, update, and run antivirus software.
- Reconnect to your network.
- Monitor network traffic and run antivirus scans to identify if any infection remains.
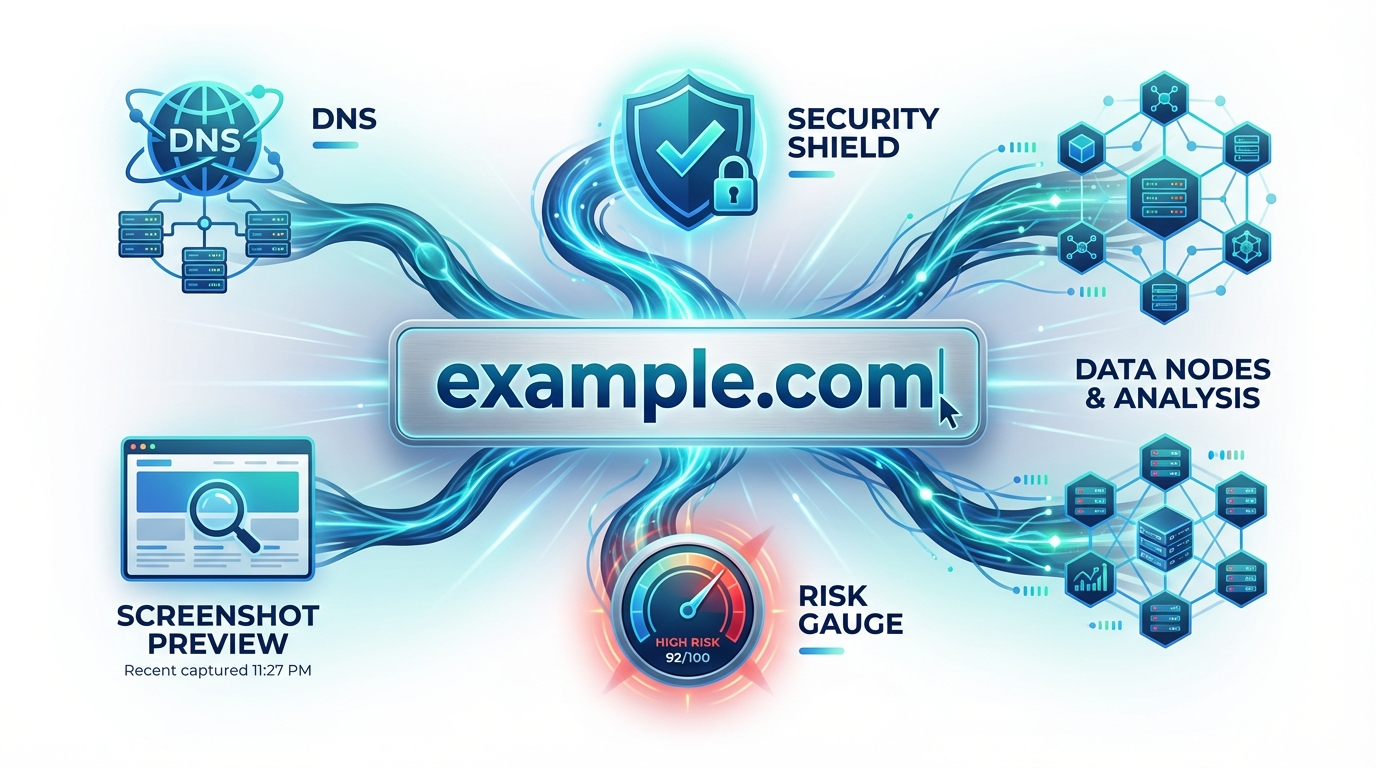
My domain name has been reported for malware, what should I do?
If your domain name has been reported for malware, you should follow the guidelines given by the source of notice (Reputation Block List provider).
The goal should be to get your domain name removed from the block list. Below, we've provided a selection of links to Reputation Block List providers and how to get your domain delisted.
Other Useful Links
- Criteria for detection for the CRDF Threat Center database
- SpamHaus FAQ
- SURBL FAQ
- WEB.DEV Safe & Secure
- CRDF: Forensic domains name investigation tools
And that wraps up the third article in our "What Is" series .
We hope you found it useful and be sure to check soon for the next instalment!
"What Is" Series article archive: