Compromised Domains - Turning Headaches Into Customer Success (And Revenue)

In last week's post, we outlined some data and metrics from a recent presentation by our CTO, Lars Forsberg.
In this post, we'll expand on the causes and the potential upside (yes, there are!) of DNS Abuse.
But first...
DNS Abuse
To make clear what this article is referring to, the definition of "DNS Abuse" used here is from the DNS Abuse Framework. The framework states that DNS Abuse is: Malware, Botnets, Phishing, Pharming, and Spam (when it serves as a delivery mechanism for the other forms of DNS Abuse).
The Data Source
The information quoted today is an extract from a unified source of DNS Abuse reports, collected from 9 different threat intelligence feeds, which are all vetted on an ongoing basis.
These feeds were selected from a list of over 200, based on their quality, low false positive rate and relative freshness of data. The feeds are: Malware Patrol, Anti-Phishing Working Group, SURBL, Spamhaus, Google Webrisk, CRDF Threat Center, OpenPhish, PhishTank, URLHaus.
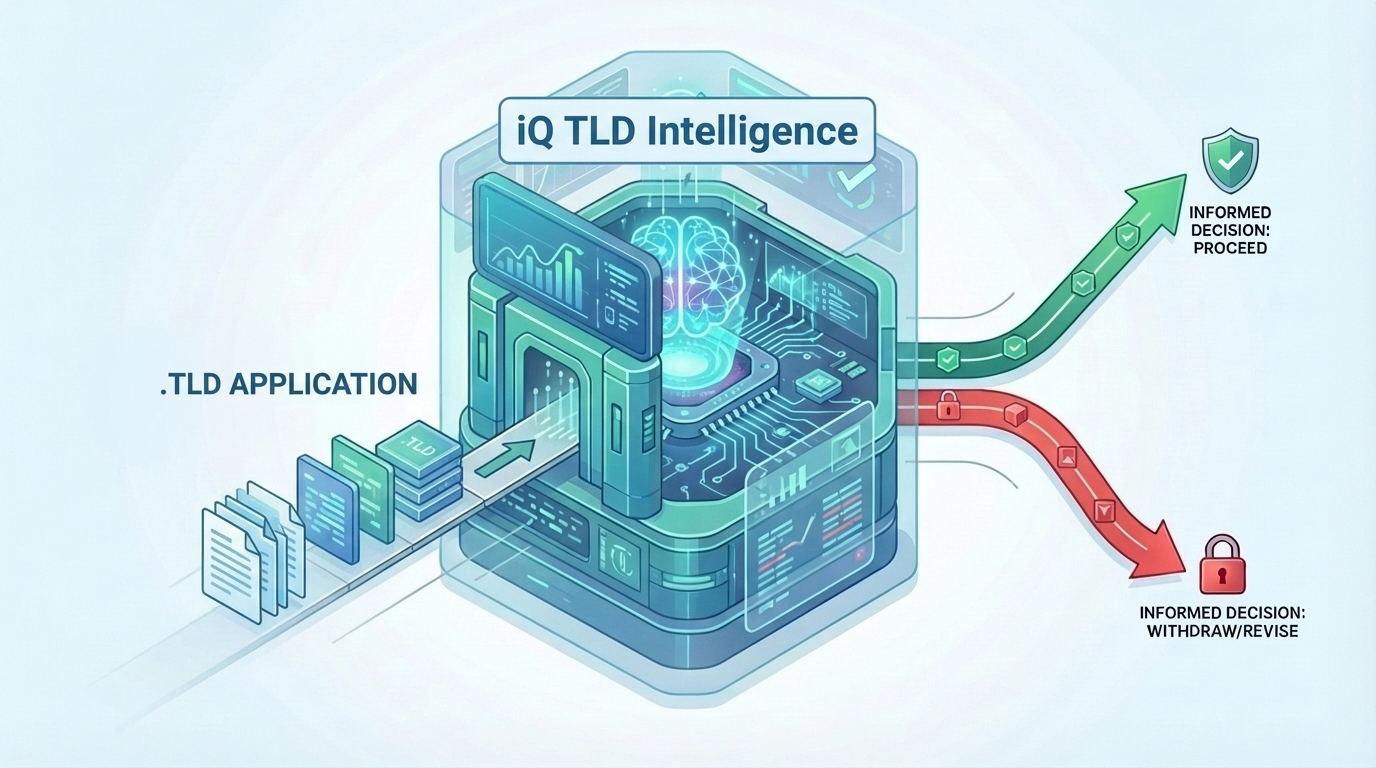
Data has been collected from these feeds since2018, with some having been added at a later date. Today, iQ uses this data source to service more than 175 TLDs, Registrars and Hosting companies. Together these organisations make up more than half the domain names registered, over 200 million.
Ok, let's get going...
Newly registered domains are not always the biggest problem
When looking at our data source, we estimate that roughly 80% of phishing, pharming and malware attacks are carried out using compromised domains. Therefore, where a legitimately registered domain name is being used.
This estimation is made based:
- the domain name not being newly registered
- has gone through at least one lifecycle (has been renewed)
- or that it has a humanly vetted, legitimate purpose on its home page while the attack is being carried out on a sub-page.
Identifying Compromised Domains
These compromised domain names come in a wide variety of types, but the
majority of them are easy to identify.
- Hacked or otherwise compromised content management systems such as WordPress (35%) and Joomla (12%) make up the bulk of them.
- Other types consist of open-source scripts that allow for uploading and executing files
- poorly secured forms
- and the list goes on...
Abuse via compromised domains complicates matters
Abuse using newly registered domains, whether it's only one or hundreds (even thousands) of generated domains, is an easier "clean". Typically (apart from any unwitting victims), sorting out the mess comprises of the Registrar and Registry working together to place the domain(s) on client or serverHold. This happens quickly and with a relatively low impact on everyone involved.
Compromised domains, via security breaches of websites, or hosting for example, are a different story. Typically these domain names reside on fully working websites of businesses, trusted organisations, personal blogs etc. The very nature that they host real information by real people is exactly why bad actors work so hard to find and exploit vulnerabilities in applications such as WordPress.
Being able to leverage the trust associated with such websites significantly increases the likelihood of them scamming someone. The chances that someone clicks on a link from a known contact are higher than a link from an unfamiliar or weird-looking domain name
The victim is usually unaware
According to w3techs.com, around 43% of all websites run on WordPress. The number of websites using WordPress in 2022 is in the region of 422 million. If we include the other CMS systems being used, such as Joomla, Drupal etc. the scale of potentially compromised websites is enormous. And that's not even factoring in staging areas, which are another very common entry point for abusive behaviours.
The beauty of systems such as WordPress is that once the initial website has been created (typically by a web developer), it "runs itself". Website owners don't need to know anything about the technology that drives it. If they can use a word editor, they can update their website. Amazing!
Unfortunately, this is also a double-edged sword. It means that website security can deteriorate quickly, especially if the web developer is not retained to make the (often frequent) necessary security updates. And when this happens, the door is wide open for bad actors to do their thing.
Worst of all, the site owner, who is busy running a business, side project etc. is typically blissfully unaware! To be fair, it's not their job or in their expertise to know. Most people assume that their website and hosting are "secure", whatever that means in their minds. And while "assumptions are the mother of all f**** ups", we would argue, not in this case. So while the website owners are happily going along with their daily lives, the bad actors are taking full advantage of the situation.
Reputation damage and loss of trust
In many cases, the first time the customer is aware of any issues is when something "bad" happens to their email or website services. Best case, they receive an email from the Hosting company informing them that they have been compromised and they need to "fix the issue". Which they usually cannot do, because their developer has left, they don't have the expertise, time or budget.
Worst case, their domain is put on serverHold and 💥💥BOOM💥💥, no more email and website. Resulting in angry exchanges between everyone involved, and the start of the erosion of trust in the service provider in the eyes of the customer. In the end, they assume (yep) a service that is available 100% of the time.
It's not all doom and gloom!
But all is not lost 😁 The customer still needs help, and as their Registrar / Hosting company, you're in the best position to do this. Both by communicating up the chain to the Registry that everything is being taken care of. And by providing solutions to fix their security problems and getting their services back online, quickly. And thus, beginning the process of (re)building trust and a stronger sense of loyalty towards you from the customer. It's not uncommon to hear of customers who had a bad experience becoming a company's biggest champion.
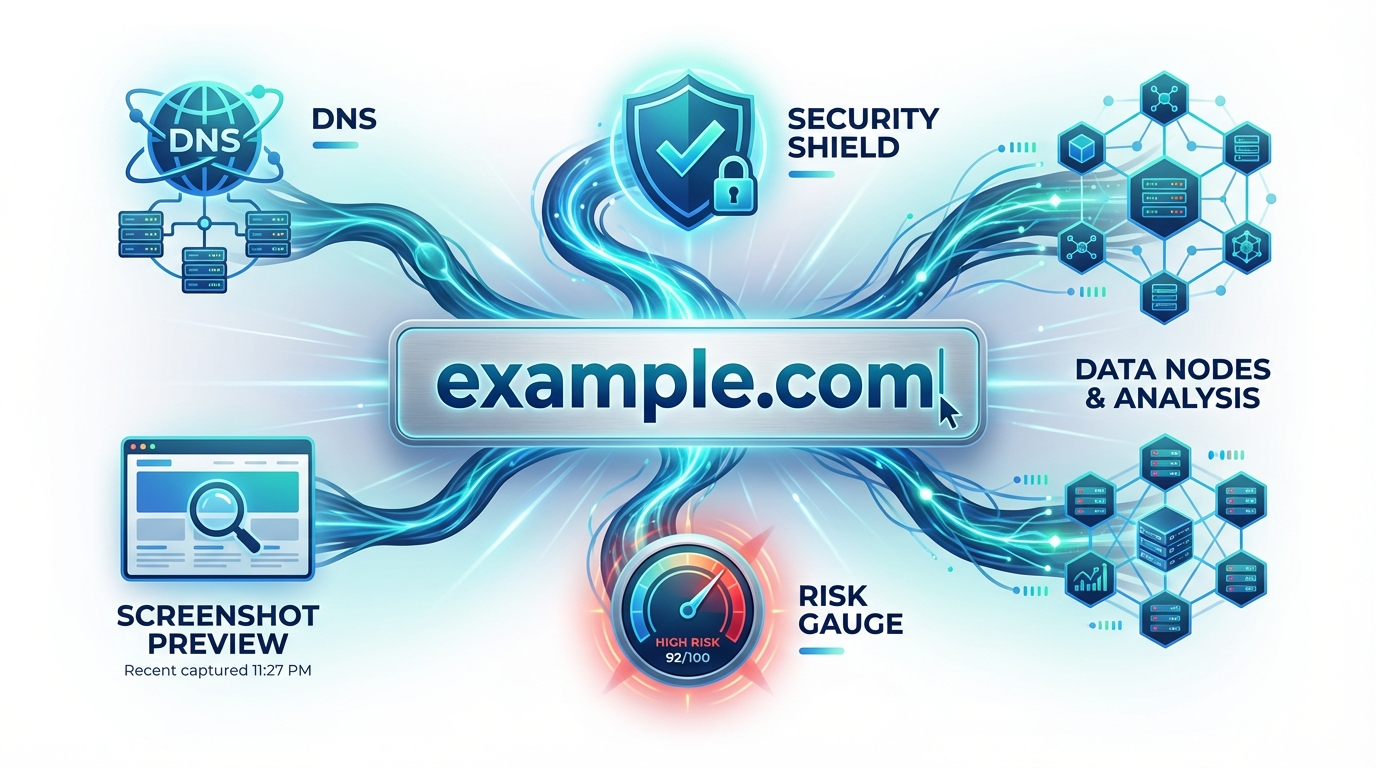
Reaction speed is critical
All of this though requires an awareness of your security situation at all times and being able to act swiftly when an issue has been identified. Monitoring and mitigation tools such as Abuse Manager and Abuse Scan, provide immediate notifications and a breakdown of what the security threat is. Arming you with the data to add to your internal systems and helping you to provide solutions to your team and customers.
Potential for revenue generation
We all know the quote that acquiring a new customer can cost five times more than retaining an existing customer. So, it's a no-brainer that acting swiftly to help a customer in need and stopping them from churning is a good thing.
But the potential benefits of a bad situation are multiple.
- There's the aforementioned customer retention and the potential to provide that customer with new services and products to prevent similar future experiences.
- Offer services such as DIFM website development. Where you can both fix the compromised website and offer an update service for a fixed monthly fee. Not only are you creating new revenue but you're also decreasing the burden on support and engineer time!
- Upsell products such as automatic backup and recovery, malware scanning, patch management, compliance products (GDRP, PCI DSS) and more.
- Brand champions. Nothing attracts other customers like someone who shares your brand name at any opportunity, for no other reason than they love what you do for them.
All offering you that golden opportunity not only to help customers in a bad situation but to also potentially significantly increase your MRR for that customer.
A WIN/WIN outcome for all!